In this article we are going to go through File Inclusion Vulnerability. Wikipedia defines File Inclusion Vulnerability as: "A file inclusion vulnerability is a type of web vulnerability that is most commonly found to affect web applications that rely on a scripting run time. This issue is caused when an application builds a path to executable code using an attacker-controlled variable in a way that allows the attacker to control which file is executed at run time. A file include vulnerability is distinct from a generic directory traversal attack, in that directory traversal is a way of gaining unauthorized file system access, and a file inclusion vulnerability subverts how an application loads code for execution. Successful exploitation of a file inclusion vulnerability will result in remote code execution on the web server that runs the affected web application."
There are two types of File Inclusion Vulnerabilities, LFI (Local File Inclusion) and RFI (Remote File Inclusion). Offensive Security's Metasploit Unleashed guide describes LFI and RFI as:
"LFI vulnerabilities allow an attacker to read (and sometimes execute) files on the victim machine. This can be very dangerous because if the web server is misconfigured and running with high privileges, the attacker may gain access to sensitive information. If the attacker is able to place code on the web server through other means, then they may be able to execute arbitrary commands.
RFI vulnerabilities are easier to exploit but less common. Instead of accessing a file on the local machine, the attacker is able to execute code hosted on their own machine."
In simpler terms LFI allows us to use the web application's execution engine (say php) to execute local files on the web server and RFI allows us to execute remote files, within the context of the target web server, which can be hosted anywhere remotely (given they can be accessed from the network on which web server is running).
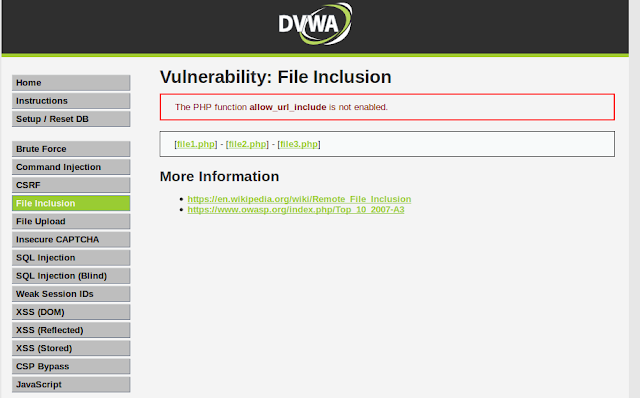
To follow along, click on the File Inclusion navigation link of DVWA, you should see a page like this:
Lets start by doing an LFI attack on the web application.
Looking at the URL of the web application we can see a parameter named page which is used to load different php pages on the website.
Since it is loading different pages we can guess that it is loading local pages from the server and executing them. Lets try to get the famous /etc/passwd file found on every linux, to do that we have to find a way to access it via our LFI. We will start with this:
entering the above payload in the page parameter of the URL:
we get nothing back which means the page does not exist. Lets try to understand what we are trying to accomplish. We are asking for a file named passwd in a directory named etc which is one directory up from our current working directory. The etc directory lies at the root (/) of a linux file system. We tried to guess that we are in a directory (say www) which also lies at the root of the file system, that's why we tried to go up by one directory and then move to the etc directory which contains the passwd file. Our next guess will be that maybe we are two directories deeper, so we modify our payload to be like this:
we get nothing back. We continue to modify our payload thinking we are one more directory deeper.
no luck again, lets try one more:
nop nothing, we keep on going one directory deeper until we get seven directories deep and our payload becomes:
which returns the contents of passwd file as seen below:
This just means that we are currently working in a directory which is seven levels deep inside the root (/) directory. It also proves that our LFI is a success. We can also use php filters to get more and more information from the server. For example if we want to get the source code of the web server we can use php wrapper filter for that like this:
We will get a base64 encoded string. Lets copy that base64 encoded string in a file and save it as index.php.b64 (name can be anything) and then decode it like this:
We will now be able to read the web application's source code. But you maybe thinking why didn't we simply try to get index.php file without using php filter. The reason is because if we try to get a php file with LFI, the php file will be executed by the php interpreter rather than displayed as a text file. As a workaround we first encode it as base64 which the interpreter won't interpret since it is not php and thus will display the text. Next we will try to get a shell. Before php version 5.2, allow_url_include setting was enabled by default however after version 5.2 it was disabled by default. Since the version of php on which our dvwa app is running on is 5.2+ we cannot use the older methods like input wrapper or RFI to get shell on dvwa unless we change the default settings (which I won't). We will use the file upload functionality to get shell. We will upload a reverse shell using the file upload functionality and then access that uploaded reverse shell via LFI.
Lets upload our reverse shell via File Upload functionality and then set up our netcat listener to listen for a connection coming from the server.
Then using our LFI we will execute the uploaded reverse shell by accessing it using this url:
Voila! We have a shell.
To learn more about File Upload Vulnerability and the reverse shell we have used here read Learning Web Pentesting With DVWA Part 5: Using File Upload to Get Shell. Attackers usually chain multiple vulnerabilities to get as much access as they can. This is a simple example of how multiple vulnerabilities (Unrestricted File Upload + LFI) can be used to scale up attacks. If you are interested in learning more about php wrappers then LFI CheetSheet is a good read and if you want to perform these attacks on the dvwa, then you'll have to enable allow_url_include setting by logging in to the dvwa server. That's it for today have fun.
Leave your questions and queries in the comments below.
Related newsThere are two types of File Inclusion Vulnerabilities, LFI (Local File Inclusion) and RFI (Remote File Inclusion). Offensive Security's Metasploit Unleashed guide describes LFI and RFI as:
"LFI vulnerabilities allow an attacker to read (and sometimes execute) files on the victim machine. This can be very dangerous because if the web server is misconfigured and running with high privileges, the attacker may gain access to sensitive information. If the attacker is able to place code on the web server through other means, then they may be able to execute arbitrary commands.
RFI vulnerabilities are easier to exploit but less common. Instead of accessing a file on the local machine, the attacker is able to execute code hosted on their own machine."
In simpler terms LFI allows us to use the web application's execution engine (say php) to execute local files on the web server and RFI allows us to execute remote files, within the context of the target web server, which can be hosted anywhere remotely (given they can be accessed from the network on which web server is running).
To follow along, click on the File Inclusion navigation link of DVWA, you should see a page like this:
Lets start by doing an LFI attack on the web application.
Looking at the URL of the web application we can see a parameter named page which is used to load different php pages on the website.
http://localhost:9000/vulnerabilities/fi/?page=include.php
../etc/passwd http://localhost:9000/vulnerabilities/fi/?page=../etc/passwd
../../etc/passwd ../../../etc/passwd ../../../../etc/passwd ../../../../../../../etc/passwd This just means that we are currently working in a directory which is seven levels deep inside the root (/) directory. It also proves that our LFI is a success. We can also use php filters to get more and more information from the server. For example if we want to get the source code of the web server we can use php wrapper filter for that like this:
php://filter/convert.base64-encode/resource=index.php cat index.php.b64 | base64 -d > index.php Lets upload our reverse shell via File Upload functionality and then set up our netcat listener to listen for a connection coming from the server.
nc -lvnp 9999 http://localhost:9000/vulnerabilities/fi/?page=../../hackable/uploads/revshell.php
To learn more about File Upload Vulnerability and the reverse shell we have used here read Learning Web Pentesting With DVWA Part 5: Using File Upload to Get Shell. Attackers usually chain multiple vulnerabilities to get as much access as they can. This is a simple example of how multiple vulnerabilities (Unrestricted File Upload + LFI) can be used to scale up attacks. If you are interested in learning more about php wrappers then LFI CheetSheet is a good read and if you want to perform these attacks on the dvwa, then you'll have to enable allow_url_include setting by logging in to the dvwa server. That's it for today have fun.
Leave your questions and queries in the comments below.
References:
- FILE INCLUSION VULNERABILITIES: https://www.offensive-security.com/metasploit-unleashed/file-inclusion-vulnerabilities/
- php://: https://www.php.net/manual/en/wrappers.php.php
- LFI Cheat Sheet: https://highon.coffee/blog/lfi-cheat-sheet/
- File inclusion vulnerability: https://en.wikipedia.org/wiki/File_inclusion_vulnerability
- PHP 5.2.0 Release Announcement: https://www.php.net/releases/5_2_0.php
- Pentest Recon Tools
- Hacking Tools 2020
- Hacking Tools 2019
- Hack Tools For Games
- Hacking Tools And Software
- Best Hacking Tools 2020
- Pentest Tools Subdomain
- Best Pentesting Tools 2018
- Hacker Tools Github
- Nsa Hacker Tools
- Hacker Tools Online
- Pentest Tools Kali Linux
- Physical Pentest Tools
- Hacking Tools For Windows 7
- Hack Tools Online
- Hack Tools Github
- Hacker Tools For Pc
- Hacking Tools Mac
- Pentest Recon Tools
- Hacker Tools Mac
- Bluetooth Hacking Tools Kali
- Hacking Tools For Windows
- Wifi Hacker Tools For Windows
- Ethical Hacker Tools
- Pentest Tools Subdomain
- Hacking Tools For Kali Linux
- Growth Hacker Tools
- Hacker Tools Windows
- New Hack Tools
- Hacking Tools For Games
- Hack Website Online Tool
- Pentest Tools
- Pentest Tools For Android
- Hacking Tools Kit
- Computer Hacker
- Easy Hack Tools
- Hack Tool Apk No Root
- Hack Tools Github
- Pentest Tools Alternative
- Game Hacking
- Hack Tools For Games
- Hacker Tools List
- Hacking Tools For Pc
- Hacker Techniques Tools And Incident Handling
- Hacker Tools Free Download
- Hacker Tools Apk
- Hack Tools
- Pentest Tools Website
- How To Hack
- Github Hacking Tools
- Pentest Tools Website
- Pentest Reporting Tools
- Best Hacking Tools 2020
- What Is Hacking Tools
- Pentest Tools Find Subdomains
- Hack Apps
- Pentest Tools Review
- Hacker Tools Hardware
- Hacker Tools Free
- Pentest Tools Port Scanner
- Physical Pentest Tools
- Hacking Tools Online
- Underground Hacker Sites
- Ethical Hacker Tools
- Hacking Tools Download
- Hackers Toolbox
- Ethical Hacker Tools
- Free Pentest Tools For Windows
- Pentest Tools Kali Linux
- Pentest Tools Bluekeep
- Hacker Tools Free
- Hack Tools For Mac
- Hack App
- Hacker Tools For Mac
- Hacking Tools For Pc
- Hacking Tools For Games
- Hacker Tools For Pc
- Easy Hack Tools
- Tools Used For Hacking
- Pentest Tools Download
- Hacker Tools 2020
- New Hacker Tools
- Pentest Tools List
- Pentest Tools Github
- Hack Tools Mac
- Game Hacking
- Hacker Tools Apk Download
- Hacking Tools Mac
- Top Pentest Tools
- Hacking Tools Windows
- Hacking Tools Mac
- Hack Apps
- Hack Website Online Tool
- Ethical Hacker Tools
- Hack Website Online Tool
- Android Hack Tools Github
- Pentest Tools Subdomain
- Hacking Tools Usb
- How To Install Pentest Tools In Ubuntu
- Hack Tools Online
- Hacking Tools For Pc
- Hacking Tools Name
- Hacking Tools Online
- Pentest Tools Bluekeep
- Hacking Apps
- Physical Pentest Tools
- Nsa Hacker Tools
- Pentest Tools Url Fuzzer
- Hacking Tools Download
- Hacking Tools 2020
- Github Hacking Tools
- Pentest Tools Windows
- Hack Website Online Tool
- Hacker Tools 2019
- Pentest Tools Website Vulnerability
- Hacker Tools Free
- How To Make Hacking Tools
- Beginner Hacker Tools
- Hack Tools 2019
- Termux Hacking Tools 2019
- Hacking Tools For Windows Free Download
- Hacking Tools Github
- Hackers Toolbox
- How To Make Hacking Tools
- Pentest Tools Android
- Hacking Tools For Mac
- Hack App
- Best Hacking Tools 2020
- Hacker Security Tools
- Hacker Tools Online
- Hackers Toolbox
- New Hacker Tools
- Pentest Tools Url Fuzzer
- Hacking Tools For Kali Linux
- Pentest Recon Tools
- New Hack Tools
- Hacks And Tools
- Hacker Tools Software
- Hacks And Tools
- Pentest Tools Linux
- Hack App
- Hacker Tools Free
- Hacker Tools Free Download
- How To Hack
- Hacking Tools 2020
- Hacking Tools For Kali Linux
- Pentest Tools Tcp Port Scanner
- Hacker Tools
- Hacker Tools For Pc
- Hacker Tools For Ios
- Hacking Tools 2020
- Hacking Tools For Windows 7
- Underground Hacker Sites
- Hacking Tools And Software
- Pentest Tools Nmap
- Hack Apps
- Tools Used For Hacking
- Wifi Hacker Tools For Windows
- Hack Tool Apk No Root
- Wifi Hacker Tools For Windows
- Free Pentest Tools For Windows
- Android Hack Tools Github
- Hack And Tools
- Pentest Tools Website
- Hacking Tools 2020
- Hacking Tools Name
- Hacker
- Hackrf Tools
- Hack Tool Apk
- How To Install Pentest Tools In Ubuntu


No comments:
Post a Comment